Computer Security Information
A software Firewall is a program that runs in the background of your PC. It monitors all connections between your PC and other systems. It will also alert you if there is a suspicious connection attempt. For example, somebody at the IP address 138.233.197.3 might be running a port scanner. Say it comes across your IP address. It will begin scanning all the ports its assigned to probe. Now without a firewall, it's quite possible that your FTP port will be open, and the program will note that in a log file as a security exploit on your PC. Now with a properly configured firewall, you would get a message something like this:
138.233.197.3 wants to talk to you, apparently for FTP. Allow it through? Y/N.
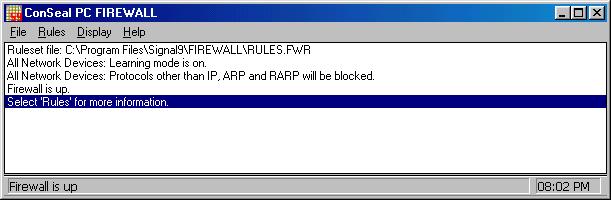
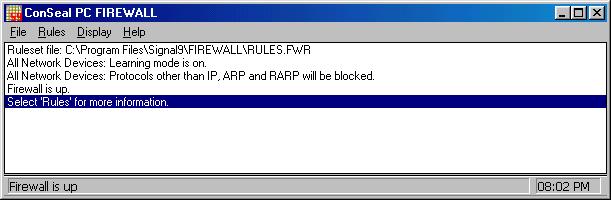
Some Firewalls just alert you so the connection can be blocked or allowed. There are, however, Stealth Firewalls, which make your PC appear offline to the Port Scanner. It does this by not responding to your PC's request for a connection. After waiting for a certain amount of time for your PC to reply to the connection request, it will move on to the next PC (or port), having assumed that your system is offline. There are many Firewalls to choose from, and it will probably seem confusing at first. If you want the protection of a firewall, but don't want to take the time to learn about them (you probably wouldn't be here if that was the case), a good solution for you is Conseal Private Desktop from Signal9 software. They also offer Conseal PC firewall, shown below. Time limit demos for both these firewalls are available at www.signal9.com.
Most firewalls allow you to configure the ruleset ( a set of "laws" for the firewall that govern what connections your PC will accept and what it will reject) manually, or use a prewritten set. Often the prewritten ruleset isn't good enough. Writing your own ruleset isn't hard, you just want to make sure you have everything covered.
Start with a good blank sheet of paper. There should be a option on your firewall for creating a ruleset (or modifying a predefined one). Always be sure to consider any programs you are running and the fact that some of them may need to connect to the web via certain ports (like ICQ). Firewalls need to be configured around ICQ, Yahoo Messenger, however, isn't affected. Also remember that you'll need to take down the firewall when playing games online.
Start off by setting the new Ruleset to block FTP connections from all addresses. This should not impair your ability to download files from FTP servers on the web, however. It should simply keep Port Scanners at bay. Now block connections from all addresses for Net BIOS. If you don't see a option for Net BIOS, try looking for TCP File Sharing- it's the same thing. Just keep in mind that if your PC is on a network, for example, at the office, Net BIOS often needs to be enabled. Consult your network manager at work before attempting any of this on a work PC.
Be sure the Firewall is set to allow Name Resolution (DNS). Without this enabled, you probably won't be able to surf the web. If your firewall has the option, be sure that ICMP nukes are blocked for all addresses as well. Call your ISP and ask if they use Identification (Ident, as it's often called) in the connection. If they do, you will need to leave that enabled. Otherwise, you should be able to block it. Also be sure to block UPD File sharing, as this is another major security bug. Again, this may be necessary if on a network. RIP and Telnet should be blocked also, without too much trouble.
If you use ICQ a lot, you may want to automatically allow all ICQ connections. This does create a small security risk, but it may be negligible to you. Remember that this is just a general guideline for configuring your firewall. I am not responsible for damages due to miss configured firewalls.
A cookie is a small bit of data, usually in a text document, which some pages will write to a designated folder in your PC. Under certain cases, some web servers will retrieve these cookies from your PC when you visit there web page, and sell the information to companies who offer products or services they think you would be interested in. These Cookies are usually stored in the directory C:\Windows\Cookies. If you have set WebPages to automatically save data, like your username or password, then these cookies are often vital. You can delete these manually, or by going to My Computer, right click on "C:," and go to properties, then click on "Disk Cleanup." Some PC's may not have this feature.
Too many times, we set our passwords as something that our four year old could probably crack. Or we set it as our social security number, or License plate number, our birth date, or our street address. Then we never change it. Never. This is just asking for trouble. Probably the most common mistake is a word followed by two numbers. This is a common pattern for passwords. Say your son's name is Robert, and he's 13. Now you set your password as Robert13. Now, the chance of somebody matching your username to this password is pretty slim. The chance that the person who is trying to hack your account is a stranger is slim, too. Say you get in a fight with somebody in a chat room. Chances are your username is also your email address, as is the case in Yahoo chat. It's more than likely if he's going to try to hack your account, he'll be using a Brute Force attack. A Brute Force program just trys ever possible password until it gets a match. It was once estimated that it would take 950 years for a brute force program to crack a 9 character random password. However, it could get a 3 character password in probably under a hour. Now consider the fact that it's quite possible that this person knows your kids first name, either because he looked it up on a People Search, or because you mentioned it. Even if you didn't mention it, the Brute Force program is going to try all those common English names, matched with numbers. If he's good, he can probably have that password within the hour. And you can say goodbye to your email account. Now take another 8 character password, using random characters instead of a word and two numbers. Say you set the new password at qmrv68xe. It's probably going to take a Brute Force program upwards of 50 years to break that. I roughly estimate that there are 1,785,793,904,896 possible combinations in a 8 character random password. And remember that the program has to wait for the server to either confirm or deny each of those passwords. It would be like sitting there and logging into your email account 100's of millions of times. He'll probably die before the program cracks your password. Now, I realize that maybe the random character password is harder to remember than your birth date, but it's not impossible. That's the problem- a good password is one you can't remember easily. Skip a round of Scrabble with your friends Saturday night, and take the time to memorize that password. You always did loose at Scrabble anyway, right?
A new wave of chain letter viruses has made the general population paranoid about email viruses, but Paranoia isn't protection. Start by skipping buying the new version of Quake for your grandson, and invest the money in a good Antivirus program, like Norton. Virus programs have a Live Update feature that allows you to get protection for your PC from the latest viruses. I recommend doing this once a week. Some Anti Virus software even has the option to automatically update every certain amount of time. Now don't get the idea that you are untouchable if you have good Virus scan software. Take the time to scan attachments before you open them- doesn't do much good if you scan them after. Now sometimes you'll get attachments like programs that are supposed to make your desktop jump and crawl all over the place. Or screensavers that are supposed to be "real footage" of some unlikely event, like your brother cleaning his room. These are breeding grounds for viruses. How many of you have open attachments from friends without scanning them first, because your friend said he scanned it. I have found viruses in things that other people said were clean. It happens. A safe alternative is to not download or open attachments. There are now viruses that can affect systems without you having to download anything- just simply view the email. If everybody would stop chain letters before they get anywhere, it would greatly reduce the surplus of viruses floating over the web. It just comes down to the fact that most chain letters aren't funny enough to warrant the virus risk.
FTP Stands for File Transfer Protocol. FTP is used to transfer data during downloads. Although FTP can be used to transfer data very quickly, it has a evil side. When a PC's FTP port is open, this gives anybody with a Port Scanner a opportunity to get into your system. An open FTP port gives them the ability to upload, download, or execute programs and files off your hard drive. Many people host FTP servers from their PC's, and there are also many FTP servers that store large amounts of data for large software companies. Probably the two biggest FTP servers are ftp.cdrom.com and ftp.download.com. A FTP server can only host files, I.E., a web page itself cannot viewed from the FTP server. Instead, companies also set up HTTP servers to store other files, such as the web pages themselves. So, you might go to www.softwarecomany.com to look for updates for your software, but you might actually be downloading the files from ftp.softwarecompany.com. There are three types of FTP servers- Anonymous, Leech, and Ratio. Large servers like ftp.cdrom.com are anonymous servers. This means that directories and files of the FTP server are not password protected, so you can download them at will. Leech servers require you to have a FTP Client. You then log into the FTP server, and are given instructions on how to get the username and password. For example, you might be required to sign up for a web service, and the username and password might be the first word of the confirmation email. People with Leech FTP servers do this often, as it creates a way for them to make money from sponsors each time someone signs up to get access to the FTP. The other type, Ratio, is a "upload" server. For Example, you might be required to upload 1 meg of certain types of files in order to be able to download 3 meg of data. So FTP has its uses, but is something that needs to be protected on your PC (see firewalls).
ICMP stands for Internet Connection Message Protocol. It is a protocol designed to confirm the connection between your PC and the server. Some ISP's use this, but it's not necessary. In certain cases, it can slow your connection.
HTTP stands for Hypertext Transfer Protocol. HTTP is the primary protocol used for surfing the web. It transfers web page data from the server to your PC.
TCP stands for Transmission Control Protocol. TCP transfers data between your PC and your dial-up server.
Net BIOS is probably the biggest security risk on an PC. Net BIOS is a web file sharing system. Unfortunately for people not using web file sharing, this poses a major security risk. Unless your PC has a firewall, the Net BIOS port is probably open. Closing this should be your major priority. It can be dealt with via a simple firewall, such as Conseal PC Firewall, available at www.signal9.com. You can also check the status of your Net BIOS port by going to http://grc.com/default.htm.
UPD is the protocol that most chat clients such as Yahoo Messenger and AOL Instant Messenger use. However useful, it has a evil side, as it's also the protocol used for backdoor access to your PC. Go to our Netstat section to see information on how to guard yourself from these.
www.signal9.com Top Rate Firewalls
http://grc.com/default.htm Excellent Site that tests to see how secure your PC is
www.download.com A excellent place to check for updates for your buggy software
http://windowsupdate.microsoft.com The source for fixes for some of Windows security bugs
www.jumbo.com A large collection of useful free software